競馬って稼げない人が大半だよね~
でも当たった時のことを考えるとなかなかやめられない!
このように競馬、その魅力に取り憑かれる者は多い。
しかし、情熱の裏には暗雲が立ち込めることも。。。
膨大な数の「競馬予想サイト」がウェブの海に存在するが、果たして全てが信頼できるものなのか?
一部には、夢を与える名の下に、正当な方法から程遠い手法を用いてユーザーの資産を奪おうとする悪徳・悪質なサイトが蔓延しているのが現状。
それでも、多くの競馬ファンが信じたいのは「真実の情報」。
彼らが探しているのは、正確な予想を提供する信頼のおけるサイトです。
私たちは競馬ファンの悩みに応えるべく、「ウマトピ」を立ち上げ、」競馬に役立つ情報サイトを作りました。
当サイトのような競馬予想サイトを検証するサイトは数多くあるものの「ウマトピ」は1味も2味も違います。
他のユーザーの評価がわかる「いいね」ボタンを設置!
競馬予想サイトに登録せず、当サイトで無料予想が見れる!
それとも自分での「予想力」を上げたいと感じる方はタメになるコラム記事もたくさんあるので合わせてごらんください。
>>競馬初心者向け記事一覧
当サイトの監修者「高森和也」の自己紹介
より詳しい監修者のプロフィールはこちらから
「本物」と呼べる競馬予想サイトの選択方法

競馬予想サイトを選ぶ上で重要なことは3つです!
- 口コミ
- 予想的中の精度
- 運営歴
上記3つが重要と言えます。
いわゆる優良競馬予想サイトと言えるサイトはサイト独自の情報を構築し、それを予想に活かしていけているサイトだとも考えられます。
これらの要素に〇がつけば重要な判断材料となりますが、現実は違います。
残念なことに世の中にある競馬予想サイトのほとんどが粗悪で悪質競馬予想サイトだといえます。
だからこそ、今回お伝えしたような抑えるべきポイントをしっかりチェックしてから利用が重要だと言えるのです!
具体的にどのような部分をチェックすることが重要なのかここから紹介していきます!
口コミは敢えて悪い口コミをチェック!
競馬予想サイトに対する口コミは競馬予想自体はもちろん、さまざまな競馬予想サイトを紹介するメディアサイトに記載されています。
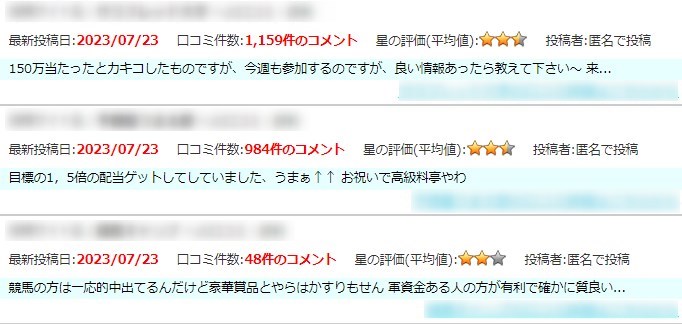
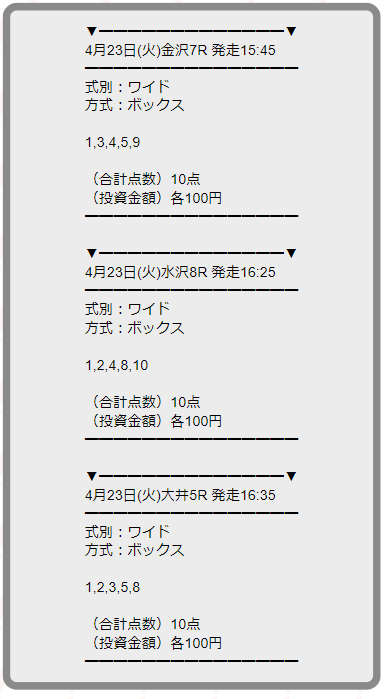
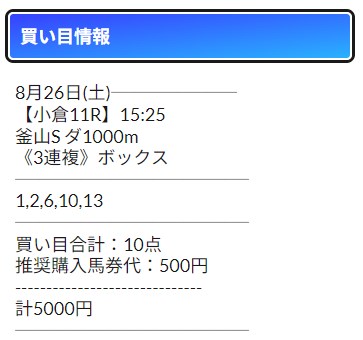
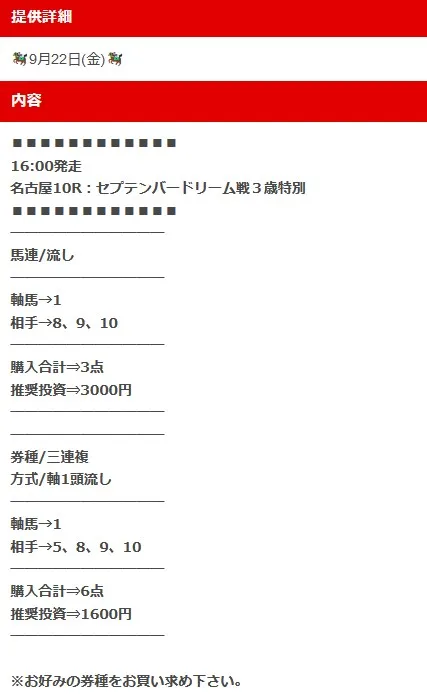
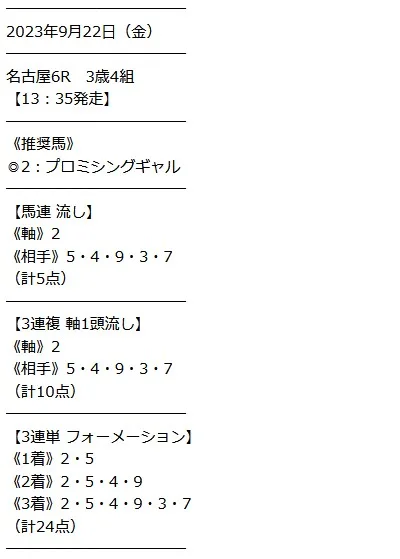
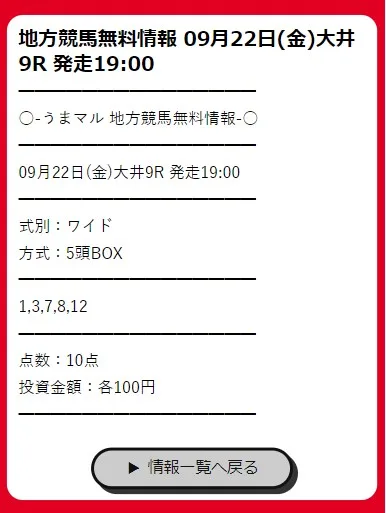
画像参考:悪質競馬予想checker
利用前に口コミが記載されているサイトから口コミを確認することが大事です!
中でも悪い口コミ(低評価な口コミ)を参考にするのがポイントです!
なぜなら良い口コミは競馬予想サイト自体の自作自演=捏造の可能性が非常に高いからです!
少しでも可能性があるであれば逆に悪い口コミを確認をし、どんなことが良くないと判断されているのかを確認しましょう!
いわゆる引き算方式です!
マイナスから入ればいざ使い始めた段階で冷静な判断ができるというものです!
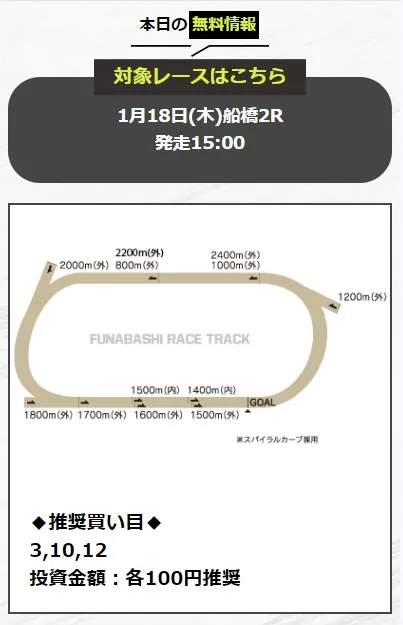
予想の精度は無料予想をチェック!
ほとんど競馬予想サイトにある無料予想を利用したことはありますか?
「どうせ無料だし、当たらないでしょう」という考えで利用したことがないという人は多いはずです!
しかし、ここが見極めのポイントなのです!!
無料予想は正直、大きな配当は見込めないです。
堅いレースや人気馬を選択してる可能性が非常に高いといえます。
しかし、その分サイトによっては手を抜いていて的中が全然しないなんていうことがあります。
だから逆を見極めるだけです!無料で的中多く出しているサイトを優良の可能性が非常に高いと言えるということですね!
とりあえず登録後、1週間~1カ月は無料予想に参加し続けることをおすすめします!そこでしっかり見極めていきましょう!
サイトの年齢をチェック
3つ目はサイト年齢をチェックすることです!
サイト年齢というのはサイトが立ち上がってどれだけの日数が経っているかという指標になります!
サイトの年数が永いとそれだけユーザーに愛されているという風にも捉えられます。
そもそもいわゆる悪質サイトというのは気づいたときには閉鎖しているところがほとんどです!(大体、半年持たない)
逆に永い運営を行っているサイトは3年以上続いてるサイトです!
こういったサイト年齢を調べられる便利なサイトがあります!
ここでは調べたいサイトのURLを入力欄に入力。
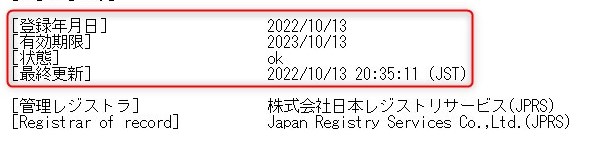
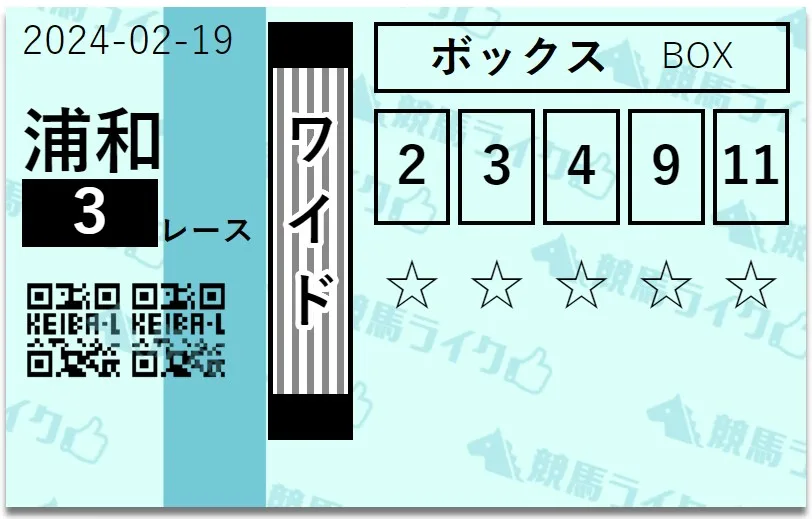
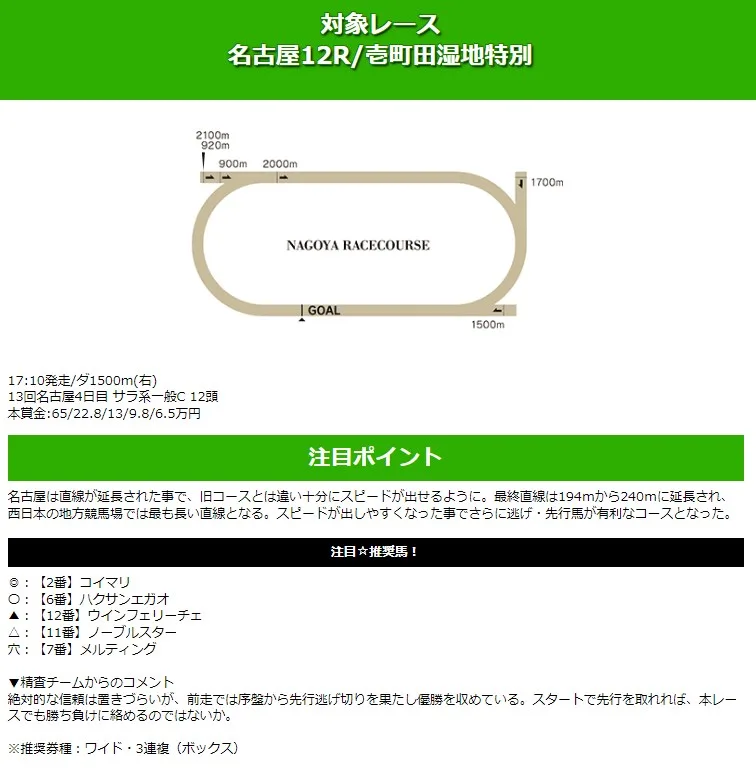
今回は当サイトでも推している競馬予想サイト「競馬ライク」を例に調査しました!
競馬ライクは2022年10月に立ち上がっていますね!約1年続いていることになります。
このようにサイトがどれだけ続いているのかも調べられる上にサイトがしっかり自分たちの情報を記載しているかルールを守っているのかということも見ることができます!
結論、競馬予想サイトは約1~3年以上続いていると長続きしている競馬予想サイトといえるではこちらもチェックしていきましょう!
ウマトピが厳選!競馬予想サイトランキングTOP10

早速ではありますが、ウマトピが実際の検証を元に厳選した競馬予想サイトを10サイト紹介していきます!
どのサイトも優秀なサイトとなっていますので是非、参考までに!
※無料情報は不定期での更新になります。ご注意ください。









もう騙されない!悪質競馬予想サイトの見極め方!

結論からお伝えすると基本的に悪質競馬予想サイトは捏造などで成り立っています!
とはいえどこでどう捏造だと判断すべきかという点は難しい部分がありますよね!
そこでここでは悪質な競馬予想サイト見極めるための方法について詳しく解説していきます。
悪質競馬予想サイトを見極めるポイントは以下の5つです!
- 的中実績に明らかな捏造疑惑がある!
- 電話番号入力を求められる!
- 口コミの捏造!
- 「絶対」「確実」という文言を使う
- 短期間での閉鎖!
数ある指標でも上記5つは重要な要素になるので、必ず覚えておきましょう!
では1つずつ詳しく解説していきます!
的中実績に明らかな捏造疑惑がある!

まず初めにお伝えするのは的中実績の捏造です!
残念ながらいわゆる悪質と呼ばれる競馬予想サイトのほとんどがサイトに記載している的中実績を捏造しています。
そもそも的中実績とはサイトが提供した予想の結果を伝えるものです。なので捏造なんてもってのほかです。
ただ、現実的に的中実績ていうのは簡単にサイト側で操作できてしまうものなのです。
悪質な競馬予想サイトはそれをユーザーのことも考えず平気で偽りの実績を記載しています。
こいう時には気になるサイトの気になる実績をチェックしてみることが大事です!
「本当に日付はあってるか」「配当はあっているのか」など確認できることは多いです!
特に、払い戻し金額が500万など大きな配当を出しているサイトは十分、注意が必要です。
電話番号入力を求められる!
これはかなり稀な例ではありますが電話番号入力を求められる場合があります。
電話番号を求められることは…本来、ないです!
なので電話番号を求めてくる競馬予想サイトは悪質競馬予想サイトだと思ってください!
口コミの捏造!
次に紹介するのも捏造関連です!
残念ながら的中実績と一緒でサイト内にあるものや競馬情報サイトなどに記載されている口コミは捏造が容易です。
あまりにも褒めている口コミを記載しているサイトは要注意です!
以前、こちらからわざわざ悪い口コミを投稿したところ後日、削除されていたことがありました。
現実、意図的に操作すぁれているサイトは存在します。注意していきましょう!
「絶対」「確実」という文言を使う
たまに見たことありませんか?
「当サイトの情報は絶対に的中します!」や「確実に高配当狙えます!」のような文言です!
このような文言の記載がある競馬予想サイトは絶対に信用してはなりません!!
なぜなら競馬に絶対はないからです!競馬はギャンブルです。
100%当たるということはありませんし、100%当たる攻略法もありません。
上記のような文言が記載された競馬予想サイトには注意しましょう!
短期間での閉鎖!
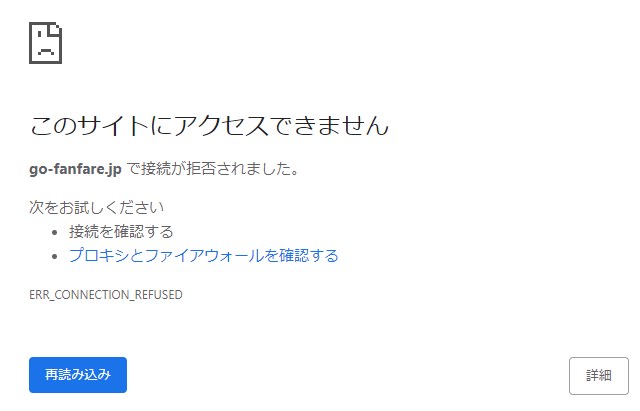
ここまでの4項目に該当している悪質競馬予想サイトは寿命も短いです。
早ければ半年で閉鎖するようなサイトもあるぐらいです。
閉鎖する前に利用していて騙されてしまっていたら元も子もありません。
なので、早い段階で見抜かれ売りゆき伸びず閉鎖してしまいます。
まとめ
競馬予想サイトはうまく活用すると自分で予想するよりも稼げるチャンスが増えるので使ってみるのもおすすめです!
しかし何度も記事内で述べましたが無理に課金したりするのは避け、無料予想などを利用し本当に良いと思ったものにだけ有料プランに参加すると望まない結果を極限避けることが可能になるので計画的な利用をおすすめいたします。
当サイトでは競馬初心者が自分で予想する力を向上させるための記事もあるので合わせてご覧ください。
>>競馬初心者向け記事一覧
>>馬券に関しての記事一覧
>>競馬予想サイトについてもっとよく知りたい方はこちらから
>>競馬の雑学